July 4, 2019
In my last post, How to create a network share in an AAD only environment, I mentioned how I have been doing some side projects for a friend’s small business and using Microsoft 365 Business to manage the Windows 10 environment. There was a need for some of the (non admin) remote users to be able to remote into a Windows 10 system at the main office so they could run a client-server application that does not run well across the WAN. In a domain environment, this is simple – open up Computer Management, find the Remote Desktop Users Group and add the necessary domain users to the group. Not so fast in an AAD only environment as we run into the same issue we did in the previous post.
Well, lucky for you, PowerShell is your friend (BTW – PowerShell is always your friend). Open up an elevated PowerShell and run the following command:
Add-LocalGroupMember -Group “Remote Desktop Users” -Member “AzureAD\mike.terrill@domain.com”
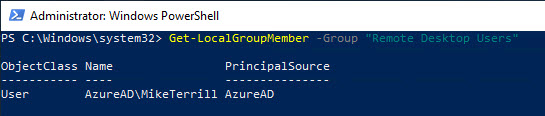
Now using the following PowerShell command, check the group membership:
Get-LocalGroupMember -Group “Remote Desktop Users”
Here we see that my AAD account was added successfully. Going into Computer Management, we see that it shows up in the UI as well:
Note that the same can be done by running the follow command from an elevated Command Prompt:
Net localgroup “Remote Desktop Users” /add “AzureAD\mike.terrill@domain.com”
Now (non admin) AAD users will be able to connect to other systems using RDP.
Originally posted on https://miketerrill.net/


Does it work with AD groups too?
That I haven’t tested as this environment is strictly AAD.
So – I could login using the old Remote Desktop client with my AzureAD account, but not with the new client. I added the AzureAD account into the RDG, and thought that this would fix it, but it doesnt for me and others. The new client still fails when trying to login with a password error “The password used to connect to the remote PC didn’t work”. Definately the right password and am a bit perplexed as to what the issue is, is there any other tweaks that you know of.
You might need to disable NLA (“Allow connections only from computers running Remote Desktop with Network Level Authentication”) and then add the following to the remote desktop connection file:
enablecredsspsupport:i:0
authentication level:i:2
Great post MIke. I would assume this would be possible to do via Intune for multiple users on devices joined to AAD ?
It should be possible via a PowerShell script delivered via Intune.
Actually that works great. Thank you.
Is there a way that to happen automatically when a machine is joined to azure ad without the need to add people manually?
You could likely do it using a PowerShell script and delivering it via Intune.
Thank you !
Thank you Sharing that me also used Azure ad Remote Desktop Users Group if a Device is Connected with Azure AD Joined